Top 10 VoIP Vulnerabilities You Must Know About
There is a peculiar characteristic about new technologies. While these are far better than the preceding ones, they turn out to be vulnerable to exploits preceding technologies were immune to.
Let's consider voice communication as an example. You could not hack or exploit the plain old telephone system without having physical access to it.
So locking up telephone terminals and switches and securing exchanges was enough for ensuring these systems were not hacked.
VoIP transformed the whole voice communication landscape. It was quick, cost-effective and offered far more features and control.
However, as VoIP operates over the Internet, it is vulnerable to a lot of internet exploits. These can be used to get into your VoIP system easily and scam you out of money or cause harm to your business.
Want your VoIP systems to stay secure? The best first step would be to learn about all the risks and vulnerabilities in VoIP Communication.
Let’s get started then, shall we?
Top 10 Risks and Vulnerabilities in VoIP Communication
When vulnerabilities and risks go unaddressed, they can result in severe financial and legal implications for your firm.
Knowing about these vulnerabilities and risks will help you secure your VoIP systems against such exploits.
Here’s the list then!
Caller ID Spoofing
Bad actors place calls from a phone number they’re not authorized to use and which don't route back to them. This is done to masquerade the origination of the call and reduce traceability.
This practice wasn’t common earlier as it was technologically intensive. However, recent years have seen a spike in such scams and the industry is locking down on it.

We have already covered this topic in detail in our STIR/SHAKEN article.
Admonition: Did you know that you can configure ConnexCS so your customers can whitelist their own CLI with an automatic call-back verification?
Call Flooding
In a call flooding attack, an attacker floods the target VoIP server with too many requests or communications. When these requests exceed the server’s capacity. It severely hinders the functioning of the server.
Call flooding attacks have 4 types depending upon what type of requests they make:
- Registration Flooding
- Call request Flooding
- Call control Flooding
- Ping Flooding
Moreover, as the server is overwhelmed handling a call flooding attack, it may not be able to tend to any genuine call requests from customers.
This results in heavy losses for the firm. They burn through resources while handling the attack and aren’t able to generate revenue from processing genuine call requests.
Having an Intelligent AnyCast Load Balancer can be helpful in dealing with such situations.
Brute Force Attack
Brute force attacks are one of the more classic ways of computer hacking. In a brute force attack, the attackers use a computer algorithm and try different combinations of usernames and passwords to gain access to an account.
While this form of attack sounds too basic, it is quite effective. Most internet users still use easy-to-guess passwords.
Once the attackers have access to your VoIP system, they can start placing calls for free. These can be sold as a grey route (non-CLI route), or for AIT.
Voice over Misconfigured Internet Telephones (VoMIT)
VoMIT presents a serious threat to the security of a VoIP system. In this case, the attackers gain access to a system, often by dictionary or brute force attacks.
They then proceed to convert voice calls into audio files and transfer these to another location. They can gain access to any and all information being shared via voice calls.
Information from recorded calls can include but is not limited to usernames, passwords, confidential information, business secrets, PINs, etc. This can use this information to further cause harm and commit more cyber crimes.
AIT: Artificial Inflation of Traffic
An Artificial Inflation of Traffic attack involves placing a large number of calls for the sole purpose of creating traffic.
The end objective is often to create billable calls (mostly via a 3rd party, with a weak association) to create a charge which will be favorable to the associated party.
AIT attacks usually take place over revenue call share numbers, short codes and premium numbers which have a cost that is to be borne by the end-user.
Traffic can also be increased in other ways. Spam messages, missed calls forcing people to call premium numbers, short codes, exploiting billing systems, sending more billing messages than permitted, etc. are the options available to attackers.
DoS/DDoS
Denial of Service (DoS) or Distributed Denial of Service (DDoS) attacks have scammers or hackers divert a large amount of malicious traffic to a voice endpoint.
A DoS/DDoS attack is another classic form of cyber attack. It overloads the servers with enough traffic that it renders the servers unfunctional or results in a complete crash.
The amount of malicious traffic can completely overwhelm a VoIP system or even just the operators rendering it incapable of handling everyday business.
The operators, thus, can lose access to their own servers and suffer from server crashes that are not only time but resource intensive to fix.
Any crucial data that may be lost during such an attack adds additional recovery costs.
Similar to Call Flooding Attacks, an Intelligent Anycast Load Balancer can help a VoIP Operator manage the attack efficiently without incuring any loses.
Phishing
Phishing calls are an extension of Caller ID spoofing and are similar to email phishing scams. Scammers impersonate appropriate authorities and extract sensitive information such as login credentials, bank details, etc. from you.
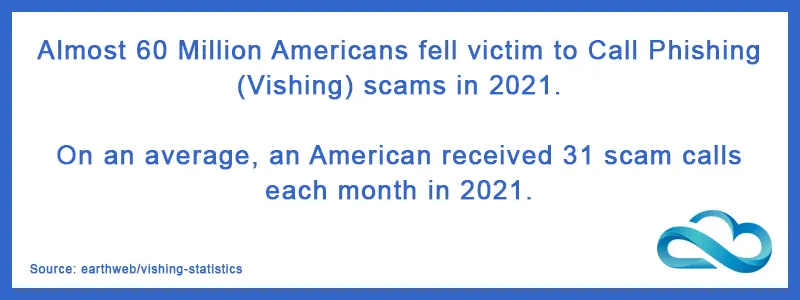
Once they have this information, they use it to gain access to your personal data, profiles, bank accounts, etc.
Phishing calls not only result in losses in terms of money but also have led to identity thefts and misuse of stolen identities for more criminal activities.
Spam over IP Telephony (SPIT)
SPIT is another VoIP scam that functions similar to an email scam. Scammers send a pre-recorded message to unsuspecting users (Voice Broadcast).
When the users pick up and listen to the entire voice message, they’re charged for the duration of the call. Although the legitimacy of Voicebroadcast can be highly dependent on the data used and circumstances.
So whilst Voice Broadcast itself may not be illegal, it is very easy for the way it is being used to be illegal.
Missed Call Traffic
All telephony providers make money from air time when there is an active call. The cost of setting up a call and tearing it down is computationally expensive.
Therefore it is undesirable to have high amounts of call setups and teardowns without any talk-time. However, there is a more illicit activity going on with missed call traffic.
It can be used to validate if a number is working or not, this is useful information for many reasons. But with spoofed CLI it can leave a call record on a victim system.
When the victim calls back it would be charged at a premium rate, which ultimately the attacker will have an affiliation with.
Out-of-Date VoIP Systems
Scammers are always on the lookout for security lapses and loopholes to exploit. The only way to protect your firm against such scams is to audit and improve your system security regularly.
However, system administrators often overlook this and do not patch their VoIP system with the latest security updates. This leaves them vulnerable to multiple forms of cyber attacks.
Some VoIP switches are advertised as “anti-hack”; this is ultimately because the system itself is insecure, but instead of fixing the route of the problem it has to be hardened by a 3rd party solution.
With that, we conclude our list of top VoIP risks and vulnerabilities!
Ending Notes
Having the right knowledge is the best start to keeping your VoIP systems safe and secure. Knowing the top attacks and what vulnerabilities they exploit can help you erect the right defences to counter them.
The industry as a whole is actively taking action to curb the nuisance of cybercriminals. However, it is always advisable to be proactive and spend wherever necessary to keep your systems secure.
So what are you going to do to secure your VoIP systems?