TLS and 2FA Security on the ConnexCS Platform
According to the financial times, telecoms fraud can cost the industry $17bn a year. With this in mind, ConnexCS strive to add as much security to our platform as possible.
We strive to make sure your data and platform are secure. Therefore we use Transport Layer Security (TLS) and 2 factor authentication (2FA) which can increase the layers of security surrounding our services.
TLS
Transport Layer Security is a security protocol which helps protect privacy and data surrounding communication over the internet. It’s primary function is to encrypt data between web applications and servers. TLS can encrypt various communications such as email and voice over IP (VoIP). All ConnexCS interfaces use TLS to encrypt communication.
To learn more about TLS check out this article from Cloudfare.
2FA Security
With an increase in cyber crime and telecoms becoming a key target area, we’ve therefore added 2 Factor Authentication (2FA) to our platform. Additional layers of security can help protect unauthorised access to your software. All of our operators will be required to use two-factor authentication when signing into the system. Two factor authentication is also available for any user accounts using RFC 6238.
2FA works by requesting an additional layer of information which usually involves requesting information a user might carry in person. This could be a code sent to their mobile phone, biometric logins or voice scans. This additional layer of security is becoming evermore popular and decreasing the chances of cyber criminals gaining access.
You or your customers can access 2FA restricted areas by using a variety of platforms including Duo, Yubikey or Google/Microsoft Authenticator.
Further developments of our 2FA now allow users (with iOS 14) to login with Face ID and Touch ID supporting Apple devices. This allows us to provide cross platform support and allows us to provide a smooth login experience regardless of device.
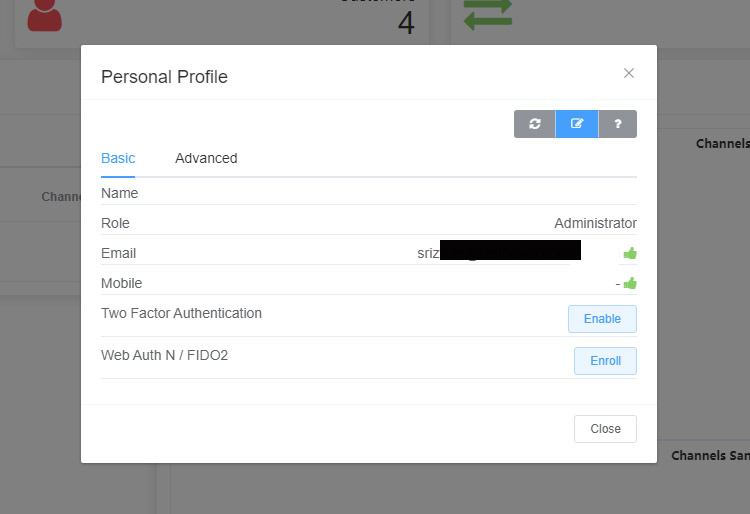
You can manage your 2FA settings within the ConnexCS control panel.
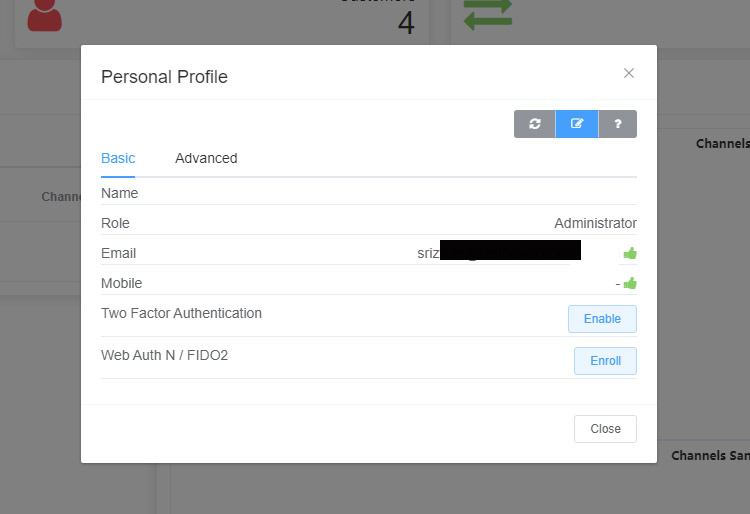
Image showcasing Two Factor Authentication in action.
Further developments of our 2FA now allow users to login with Face ID and Touch ID supporting Apple devices. This allows us to provide cross platform support and allows us to provide a smooth login experience regardless of device.
If you’d like to learn more about the protective measures we put in place or any of our Class 4 or Class 5 solutions, feel free to get in touch on the following details.